And much more
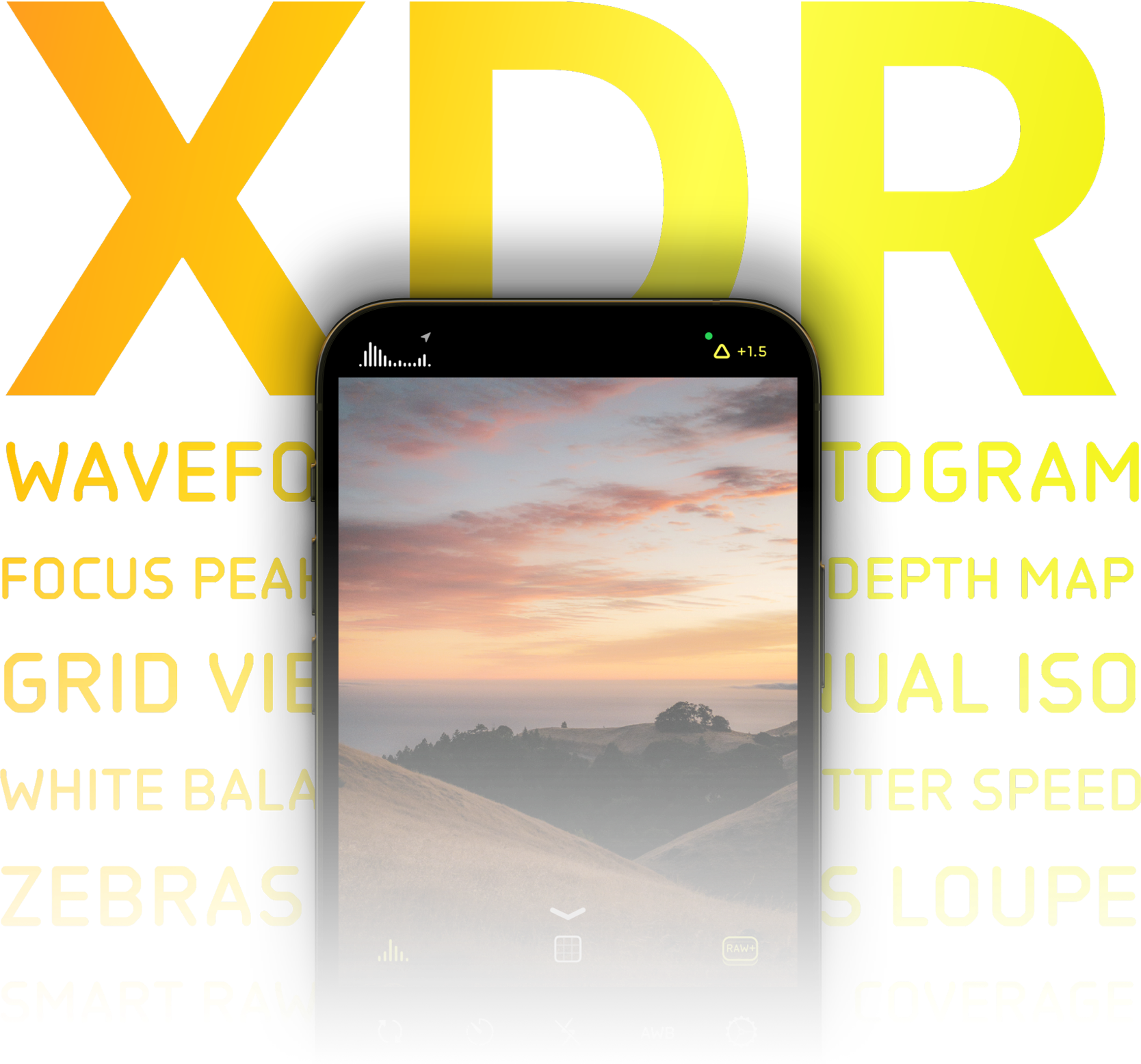
Process Zero is just one of our many latest and greatest features that we've rolled out to users over the last seven years. Check out some of the new updates:
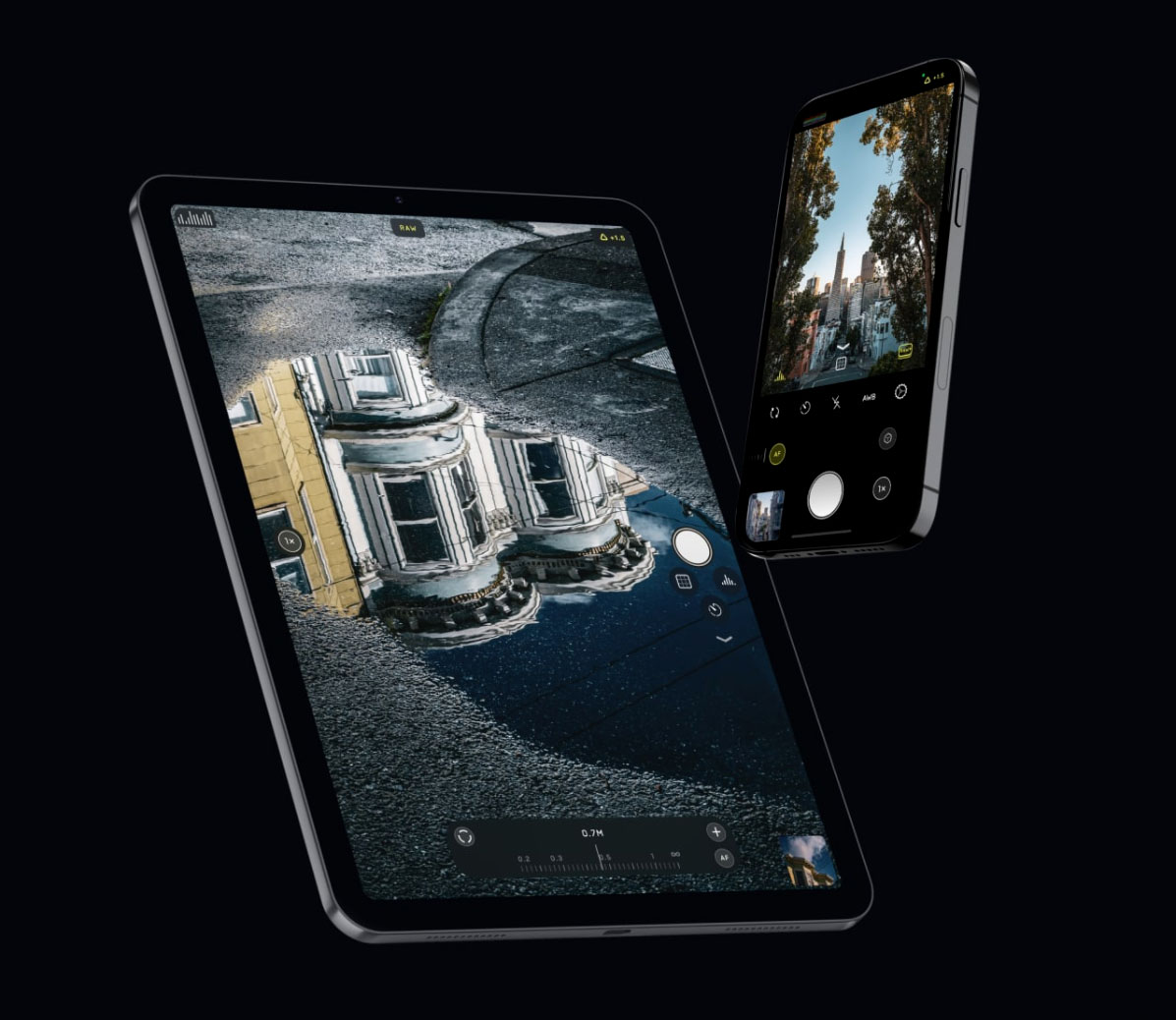
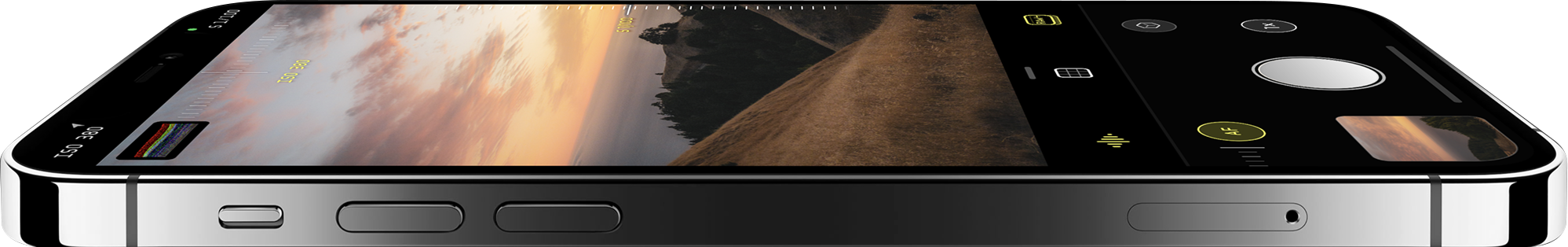
Updated for the latest and greatest devices and built for the newest version of iOS.
lux.camera
The CISA Vulnerability Bulletin provides a summary of new vulnerabilities that have been recorded in the past week. In some cases, CISA (.gov)
: Large archives are sometimes split into parts; while modern versions use .rar and .rev , older systems used sequences like .rar , .r00 , and .r01 . Safety and Potential Risks
Specific information regarding a file named is not readily available in public databases or documented internet mysteries. In general computing terms, a file with this extension is a Roshal Archive (RAR) , a proprietary format used for data compression and file spanning.
Because "52374.rar" uses a generic numerical name, it is often characteristic of files found on file-sharing sites, peer-to-peer networks, or as automated email attachments. Vulnerability Summary for the Week of CISA
If you encountered this specific file, it is important to understand what it likely represents and the risks associated with such downloads. Understanding RAR Files
52374.rar
The CISA Vulnerability Bulletin provides a summary of new vulnerabilities that have been recorded in the past week. In some cases, CISA (.gov)
: Large archives are sometimes split into parts; while modern versions use .rar and .rev , older systems used sequences like .rar , .r00 , and .r01 . Safety and Potential Risks 52374.rar
Specific information regarding a file named is not readily available in public databases or documented internet mysteries. In general computing terms, a file with this extension is a Roshal Archive (RAR) , a proprietary format used for data compression and file spanning. The CISA Vulnerability Bulletin provides a summary of
Because "52374.rar" uses a generic numerical name, it is often characteristic of files found on file-sharing sites, peer-to-peer networks, or as automated email attachments. Vulnerability Summary for the Week of CISA In general computing terms, a file with this
If you encountered this specific file, it is important to understand what it likely represents and the risks associated with such downloads. Understanding RAR Files